How Does Unlimited Access To AI Tools Transform User Creativity?
Focus on
The Rise of Nanotechnology: How Small is Powerful
Imagine a world where medical treatments could be delivered directly to diseased cells, where electronic devices could be manufactured atom by atom, and materials could be designed to possess specific properties at the nanoscale. This is not the realm of science fiction, but an emerging reality made possible by nanotechnology. This technology, which operates at the scale of a billionth of a meter, is gradually revolutionizing various industries, from healthcare to electronics, to environmental conservation. In this article, we delve into the rise of nanotechnology, exploring its origins,...
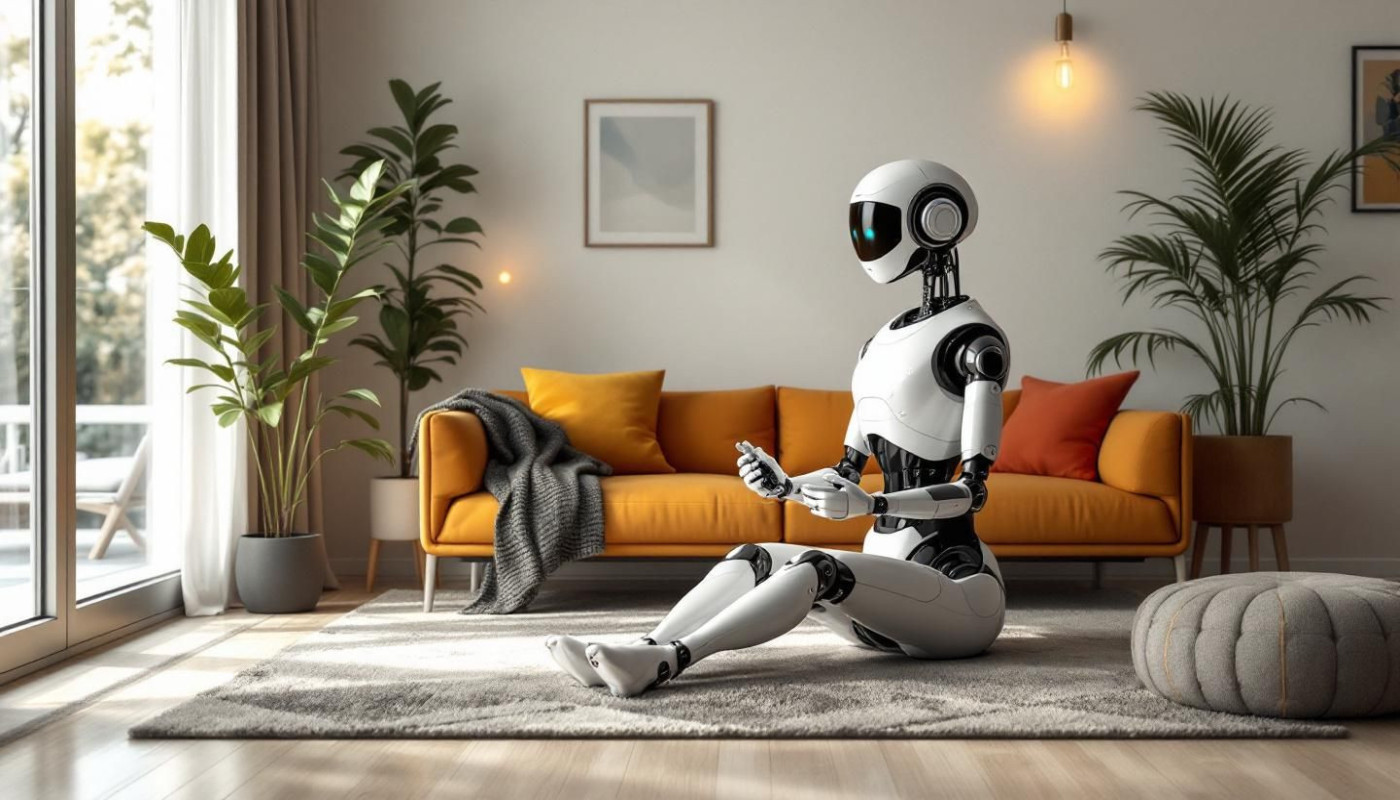
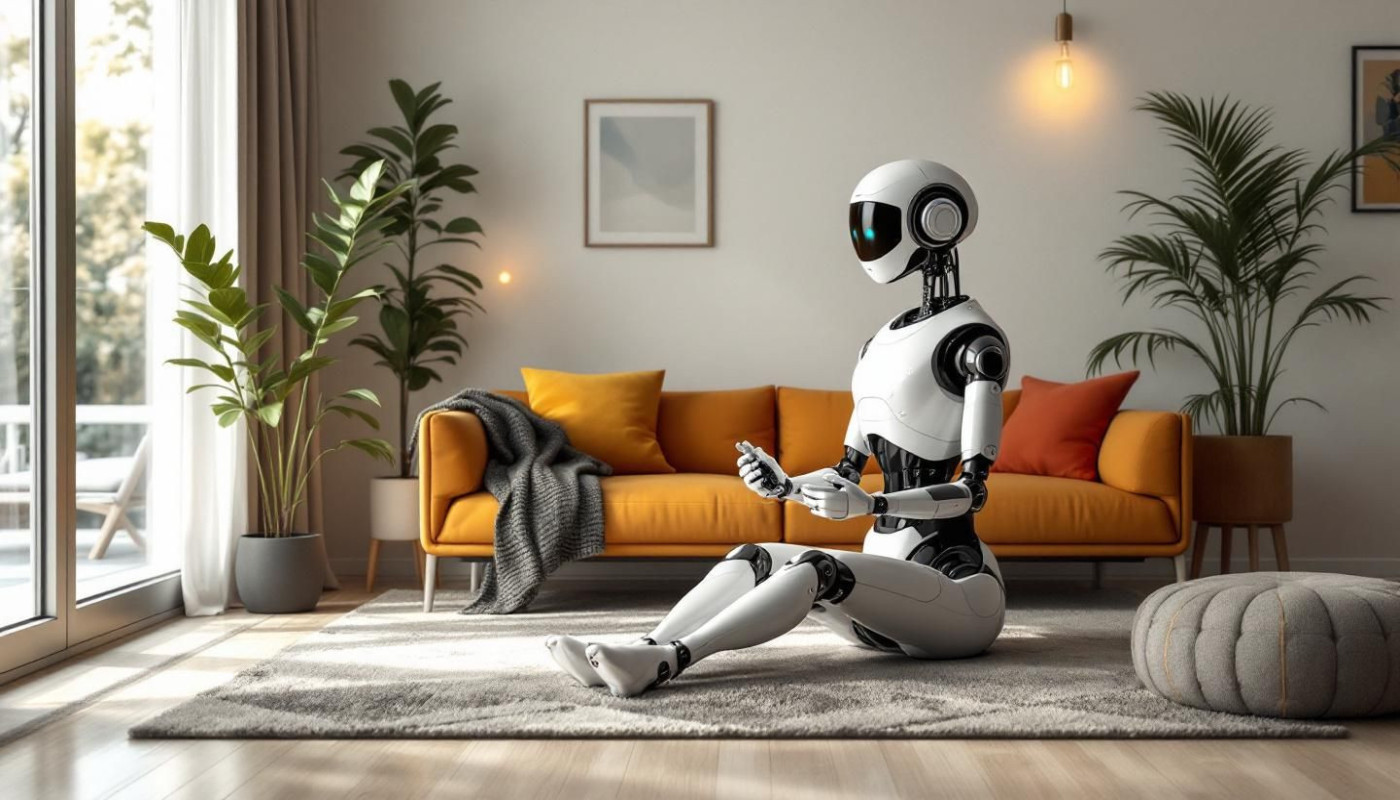
How Personalized AI Companions Enhance Daily Interaction?
In a world where digital experiences are increasingly tailored to individual needs, personalized AI companions are transforming the way people interact with technology on a daily basis. These intelligent systems learn from users’ habits, preferences, and routines to provide support that feels both intuitive and genuinely helpful. Explore how these innovative companions are enhancing communication, productivity, and well-being—offering a glimpse into a future shaped by seamless human-AI collaboration. The following paragraphs invite you to discover the many ways personalized AI companions can positively influence daily life. Personalization redefines user engagement Personalized interaction lies at the heart of next-generation AI technology, fundamentally transforming the way users...
In the spotlight
Streamlining Field Trials: The Impact Of Digital Solutions On Agronomy
In the ever-evolving landscape of agricultural technology, the advent of digital solutions has revolutionized the way field trials are conducted. With the potential to enhance the precision and efficiency of agronomic research, these innovative tools are reshaping the industry. Dive into the world of modern agriculture to explore how digital solutions are making a significant impact on the management and outcome of field trials, promising a future of smarter farming. This exploration beckons a closer look at the transformative effects digital technology brings to the field of agronomy. Revolutionizing Data Collection The advent of digital solutions in the realm of agronomic field trials has markedly transformed the methodology behind data collection. Where traditional practices were...
Recent